The story:
Some time ago I tried to charge my powerbank (20000 mAh). I just grab "no-name" charger and some "no-name" cable and start to charge. I took all night to charge it from 0 to 100%. I though this is normal, big powerbank, long time. Later, I tried to charge the same powerbank from 0 to 100% using the same "no-name" charger but with better (let's say "branded") cable. And the charging time was significantly better. I decided to use "branded" charger and "branded" cable and charging from 0 to 100% again. And it was faster than in previous two trials. So I started to read about charging standards, how cable can affect the process and so on.
The theory:
We have "USB standards" and "prioprietary specifications" in terms of charging.
USB standards are:
1. Standard USB port i.e. in PC
When connected and transferring data we can charge devices with different power depend on USB type:
- USB 1.0 gives 0.1A with 5V which gives 0.5W
- USB 2.0 gives 0.5A with 5.0V which gives 2.5W (from 2000)
- USB 3.0 gives 0.9A with 5.0V which gives 4.5W (from 2008)
- USB Type-C gives 1.5A/3.0A with 5.0V which gives 7.5/15.0W (from 2014)
2. Battery Charging (BC) 1.1/1.2
In year 2000 and up USB 2.0 with its 2.5W was not enough. In 2007 a Battery Charging 1.1 (BC 1.1) specification was released. It defined three new types of ports:
- Standard Downstream Port (SDP) - USB 2.0 compatible in terms of power (2.5W)
- Dedicated Charging Port (DCP) - does not support data transfer, used only for charging. Support max 1.5A with 5.0V which gives max 7.5W
- Downstream Port (CDP) - allows both data transfer like USB 2.0 and charging like DCP
In 2010 a Battery Charging 1.2 (BC 1.2) specification was released, where 1.5A was increased to 5A, which gives max 25W using 5.0V.
3. Power Delivery (PD) 1.0/2.0/3.0
In 2012 Power Delivery 1.0 specification was released. It introduces so called source profiles:
- 5.0V with 2.0A which gives 10W (profile 1)
- 12.0V with 1.5A which gives 18 W (profile 2)
- 12.0V with 3.0A which gives 36 W (profile 3)
- 20.0V with 3.0A which gives 60W (profile 4)
- 20.0V with 5.0A which gives 100W (profile 5)
In 2014 Power Delivery 2.0 specification was released (as a part of USB 3.1 and USB Type-C). Comparing to PD 1.0, 12V is gone and 9V and 15V are introduced. Source profiles no longer exist - they were replaced by power rules. Power rules keep fixed voltage but allow to negotiate current level, which gives different power level:
- 5.0V with 0.1A - 3.0A which gives 0.5W - 15W (rule 1)
- 9.0V with 1.67A - 3.0A which gives 15W - 27W (rule 2)
- 15.0V with 1.8A - 3.0A which gives 27W - 45W (rule 3)
- 20.0V with 2.25A - 3.0A / 3.0A - 5.0A (using rated cable) - 45W - 100W (rule 4)
In 2018 Power Delivery 3.0 specification was released. It does not change power rules introduced in PD 2.0 but adds some features like Programmable Power Supply (PPS) which allows configure voltage in 20mV granular increments.
4. Prioprietary specifications
- Qualcomm Quick Charge (QC 1.0/2.0/3.0/4.0/4+)
- MediaTek Pump Express
- Samsung Adaptive Fast Charging
- Oppo VOOC (named Dash Charge/Warp Charge on OnePlus devices and Dart Charge on Realme devices)
- Huawei SuperCharge
The test:
Lets have a look how it looks like in real life. I will charge those devices:
- Tablet Lenovo Tab2 A10-70L
- Xiaomi YDDYP01 20000mAh power bank
- Xiaomi Redmi 5 Plus smartphone
- Xiaomi POCO X3 NFC smartphone
- Aukey PB-XD26 26800mAh power bank
- Sony Xperia 10 III smartphone
I will use chargers:
- Aukey PT-Y11 wall charger which have to ports: USB-A supports Quick Charge 3.0 (18W) and USB-C supports Power Delivery 3.0 (30W).
- Xiaomi POCO X3 stock charger delivered with the phone.
- Sony Xperia 10 III stock charger delivered with the phone.
I will use cables:
- 1m Aukey USB-A/micro-USB
- 1m Aukey USB-A/USB-C
- 1m Aukey USB-C/USB-C (rated for 100W for PD 3.0)
I will use testers:
- Fnirsi FNB28 for USB-A
- Fnirsi FNC88 for USB-C
Results:
1. Lenovo Tab2 A10-70L
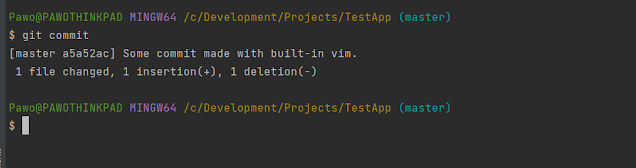
Connection: Aukey PT-Y11 USB-A -> Fnirsi FNB28 -> USB-A/micro-USB -> Lenovo Tab2 A10-70L
Power measured: 10W
I cannot find if it is compatible with any proprietary specification, but 10W suggests it is Qualcomm QC 1.0. Tester does not recognize it as Qualcomm QC 1.0, intstead it showh Batery Charge 1.1 DCP standard.
2. Xiaomi YDDYP01 20000mAh
Connection: Aukey PT-Y11 USB-A -> Fnirsi FNB28 -> USB-A/micro-USB -> Xiaomi YDDYP01 20000mAh.
Power measured: 18W
Accroding to this device specification it is compatible with Qualcomm QC 2.0 and tester recognizes it indeed as Qualcomm QC 2.0 12V
3. Xiaomi Redmi 5 Plus (smartphone was initially charged about 30% during the test)
Connection: Aukey PT-Y11 USB-A -> Fnirsi FNB28 -> USB-A/micro-USB -> Xiaomi Redmi 5 Plus
Power measured: 14W
The device is based on Qualcomm Snapdragon 625 which is in theory Qualcomm QC 3.0 compatible (according to specification of this chipset). However tester recognizes it as Qualcomm Quick Charge 2.0 9V, so I suspect that smartphone manufacturer "downgraded" charging to QC 2.0 in order not to pay higher license fo QC 3.0,
4. Xiaomi POCO X3 NFC (smartphone was initially charged about 85% during each the test)
Test 1:
Connection: Aukey PT-Y11 USB-A -> Fnirsi FNB28 -> USB-A/USB-C -> Xiaomi POCO X3 NFC
Power measured: 16W
The device is based on Qualcomm Snapdragon 732G which is in theory Qualcomm QC 4+ compatible (according to specification of this chipset). Tester recognizes it as Qualcomm QC 3.0 which is OK because charger is QC 3.0 compatible and QC 4+ device is backward compatible with QC 3.0
Test 2:
Connection: Aukey PT-Y11 USB-C -> Fnirsi FNC88 -> USB-C/USB-C -> Xiaomi POCO X3 NFC
Power measured: 14W
QC 4+ is compatible with Power Delivery (and can give max 27W), so charging with PD port of this charger simply works. However tester recognizes it as Huawei SCP standard.
Test 3:
Connection: Xiaomi stock charger USB-C -> Fnirsi FNB28 -> USB-A/USB-C -> Xiaomi POCO X3 NFC
Power measured: 20W
Xiaomi stock charger has max 27W, so it is QC 4.0 compatible, however tester recognizes it as QC 3.0.
5. Aukey PB-XD26 26800mAh
Connection: Aukey PT-Y11 USB-C -> Fnirsi FNC88 -> USB-C/USB-C -> Aukey PB-XD26 26800mAh
Power measured: 30W
According to specification of this power bank it is PD 3.0 compatible and its max charging power is 45W. Used charger has max 30W output via its PD port, so charging works with its maximum speed due to charger limit (limited to 30W by charger). However tester does not recognize it as Power Delivery standard.
6. Sony Xperia 10 III
Test 1:
Connection: Aukey PT-Y11 USB-A -> Fnirsi FNB28 -> USB-A/USB-C -> Sony Xperia 10 III
Power measured: 7W
The device is based on Qualcomm Snapdragon 690 5G which is in theory Qualcomm QC 4+ compatible (according to specification of this chipset). But this phone does not support any QC standard (probably due to licensing costs). Moreover stock charger delivered with the phone gives also max 7,5W power.
Test 2:
Connection: Aukey PT-Y11 USB-C -> Fnirsi FNC88 -> USB-C/USB-C -> Sony Xperia 10 III
Power measured: 15W
In theory this Sony phone can take 30W via PD. I have never achieved such value, I was able to get 18W max.
Final notes:
- The simple truth is: the more power (W) delivered, the faster charging.
- Charged device and charger should be compatible with the same charge standard.
- USB cable used for charging must have good quality too.
- Those USB testers used are not always reliable in my opinion:
- they do not properly recognize charging standards (especially PD, QC 4.0)
- sometimes I had to connect them second or third time to start charging i.e 18W not 10W. It looks like sometimes "handshake" between charged device and charger with tester plugged in between does not work (or works depending on the connection order...)